Hey guys, what is up. In this particular post, we will be talking about what is network security. How its work and what are the types of network security.
Updated on 05.10.2021
KEY POINTS
What is network security?
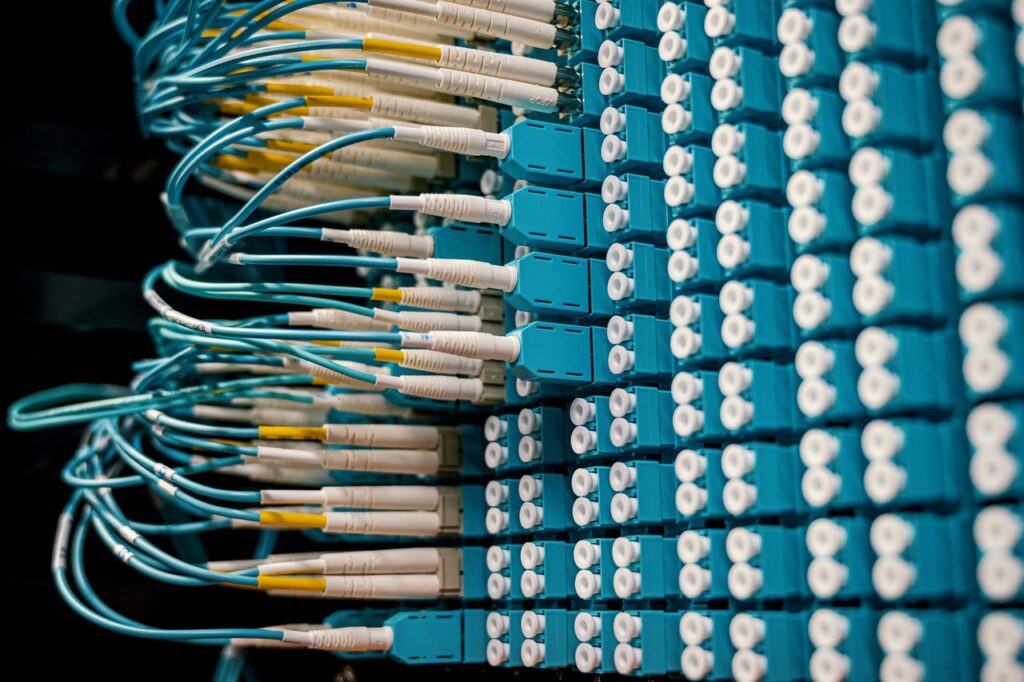
Network security is the task planned to protect the utility and integrity of your data and network. It is the exercise of protecting and preventing unwanted attacks from unknown sources into the corporate web. The main purpose of this is to ensure endpoint security, which focuses on every device, instead of focusing on how each device communicates with each other or joining material between them. private message
- It aims at the number of attacks.
- It prevents them from entering and spreading on your web.
- Productive network security manages approach to the web.
The main aim of network security is to protect your web and connected devices from threats caused by hackers.
How does it works?
Network security merges some layers of defenses at the boundary and in the web. Each layer carries out a set of policies and controls. Allowed users attain access to network resources, but malicious attacks are blocked that can create threats to the resources.
The fundamental principle of network security:
- Protection: Configure your devices and web as correctly as possible
- Spotting: You should be able to recognize when the configuration settings are changed or when some network traffic shows an issue.
- Reaction: After recognizing an issue, the web should react to them and come back to a safe state as quickly as possible.
Benefits of using network security:
Digitalization has changed our lifestyle. How we work, live, play, and learn all things have changed. Every firm that provides services that consumers and workers must protect their web from malicious attacks. It also helps you to save important data from attacks.
Types of network security:

- Access control: The system should be able to block unauthorized users and devices from using your data and resources. Approved users should be allowed to access the data and network to their work with the limited number of resources for which they are allowed.
- Anti-malware: Viruses, trojans, and worms try to expand across a web and can leak data from inoperative machines for weeks. Anti-malware applications should do their best by preventing the initial infection and also eliminate out the virus that makes its way into the network.
- Application security: Unsafe applications are the root cause by which hackers get access to the network. There is always a need to secure those apps by the means of hardware and software.
- Data loss prevention: Human beings are surely the weakest security connection. There is a need to apply technologies and processes that guarantee that the workers don’t intentionally or by mistake send some private/ sensitive information outside the web.
- Email security: Hacking is one of the most usual ways by which hackers get access to the web. Email safety tools block all incoming or outgoing messages that contain sensitive information. Also, these tools block messages that can harm the web.
- Web security: In this, we need to be able to check internal worker’s network use in order to stop network threats. By using browsers that can affect the web.
Types of security using tools or applications:
- Firewalls: Firewalls are one of the finest applications of the web security world. They obey the rules that we define to allow or deny traffic at the border between your web and the internet. By creating an obstacle between the trusted zone and the unauthorized zone.
- Mobile device security: Hackers are increasingly attacking mobile devices and apps. Wireless devices have all the possible security defects of another network gadget. In the upcoming time, you will be able to control which devices can approach our web.
- VPN: A virtual private network is a tool that verifies the interaction between a device and a secure web, making a secure path across the internet.
In the upcoming post, you will be getting information related to loops in c++. If you haven’t read about what is deep learning, then go and read this. You can also read previous posts by scrolling downwards. Also, stay tuned for the upcoming post.


Very interesting, knowledgeable and useful
Grt